What is OpSec?
For normal people we can define it like this: basically you need to not leave about bits of information that can be traced back to you, or be put together like a puzzle to form a bigger picture about who you are or what you are doing. Don’t use credit cards in your name, sign up for social networks, and post pictures with Exif data or landmarks in the background. These types of acts leave a trail right back to the person. Other ways to practice OpSec might be to not give people your personal information, your back account information, or even share your passwords. The biggest way I feel people destroy their OpSec is by telling people what they are doing. Many people trust others with little thought to how the information they are giving them can be used to betray them.
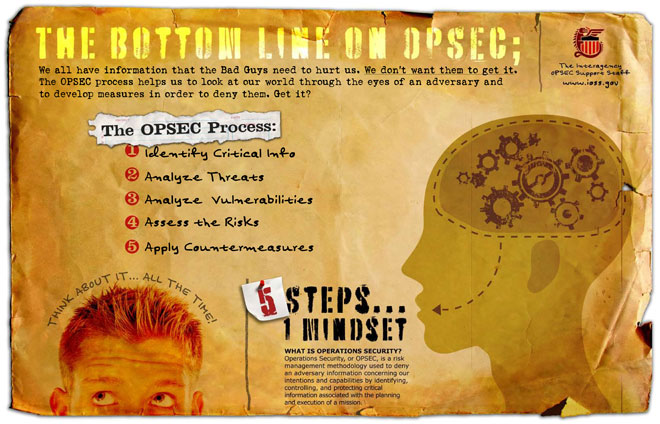
The military defines OpSec with a very structured definition. “Operations security (OPSEC) is a term originating in U.S. military jargon, as a process that identifies critical information to determine if friendly actions can be observed by adversary intelligence systems, determines if information obtained by adversaries could be interpreted to be useful to them, and then executes selected measures that eliminate or reduce adversary exploitation of friendly critical information.”
Who uses OpSec?
When we look at how the term has changed in the last 10 years, we can add in many types of situations. Businesses use it to protect their R&D and product lines. Law Enforcement uses it in investigations to build cases against criminals. Hackers use it to keep from getting arrested, and terrorists use it to keep their plans secret. OpSec is used by so many types of organizations that it has become a daily practice. Many groups use VPN, Tor, or other types of technology to hide their traffic or actions.
I have great OpSec! How can I fuck it up?
There are many ways to fuck up OpSec. When we look at some of the most highlighted hackers who have gotten caught these last few years we notice a couple of things. They did not practice good enough OpSec. Most of these hackers slowly leaked information that was used to trace or correlate them to their traffic or habits. This eventually led to their arrest and was used as evidence against them.
Many people say to use Tor (The Onion Router) to create a VPN to hide your activities. As many have found out this is completely false. Law enforcement and criminals alike use and operate on Tor or VPN services. Tor is not secure (it leaks your location, and stands out like sore thumb) and is enough to get you looked at. VPNs are not secure either. Both VPN operators and Tor exit nodes can see what’s going through the pipe. In one case the government used an Adobe flaw to connect outside of the Tor network and reveal the users IP address.
No one can honestly say that they use the best OpSec that’s out there. What’s safe today may not be safe tomorrow. When traveling the internet, you connect through many systems and it is impossible for anyone to tell if those system are secure, uncompromised, or that the owner isn’t doing malicious things to the traffic. While we all use software, it’s not as secure as we think. Bugs, tech issues, and other flaws exist in the product line, which may leak your usage.
Here are a few other ways to screw up your OpSec:
- Doing operations from your house or work
- Using the same MAC address for multiple operations
- Using the same Internet handle for both personal and operations work
- Working with others who will sell you out to save their ass
- Bragging about your operations
There are so many ways to screw up your OpSec and the list grows longer every day.
Let’s look at a few people that fucked up their OpSec. Many stories have been written about each of these people. Some stories are more accurate than others.
In the case of the group known as YardBird, they used a common encryption key that was given to all members. While this allowed them to kill a key and replace it quickly, it took only one member getting caught and giving up the encryption key to expose a portion of the group. Once the police had the key they could read messages meant for the group.
“During a period of 15 months, there were around 400,000 images and 11,000 videos uploaded to a central server run by the group and shared by the members. The reason we know that, is because during that 15 months, the FBI performed an undercover operation to infiltrate the group in hopes of apprehending the members. They successfully apprehended 1 in 3 members of the group. One of those who remain free to date, was the leader of the group, who also went by the online name YardBird.
How is it possible that after so much effort was put in by the American Federal Bureau of Investigation (FBI), the Australian Federal Police (AFP) and the Australian Queensland Police Service, that people high up on the wanted lists were able to evade capture. They used strong cryptography, and proper OpSec rules.”
Link: The YardBird Story
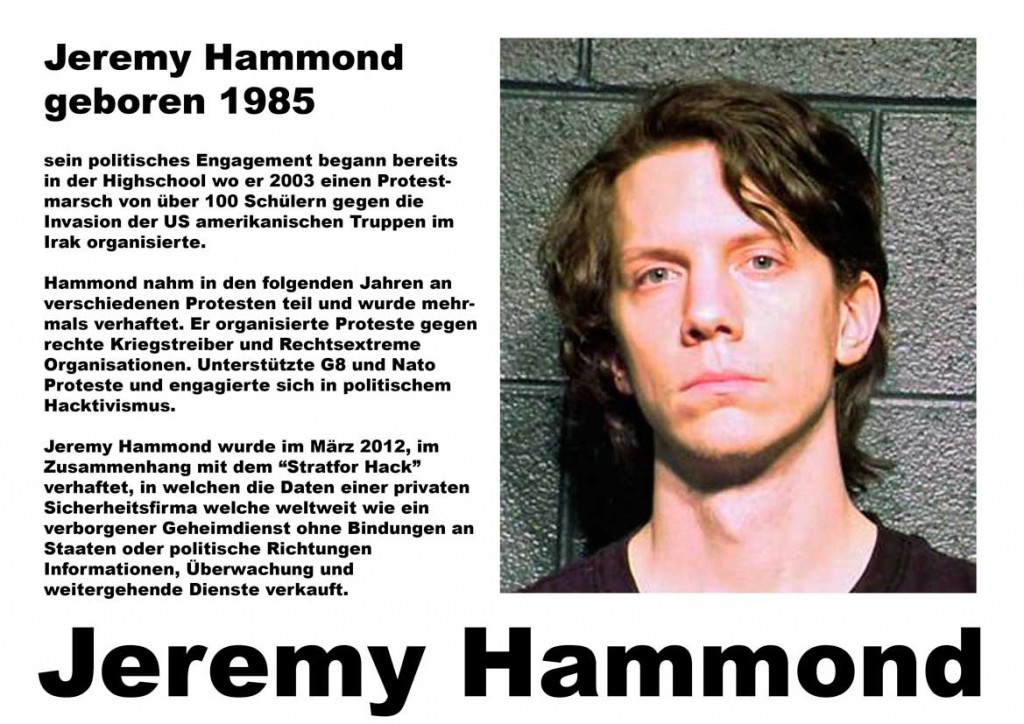
Jeremy Hammond had pretty good OpSec, but was working with an informant: Hector Xavier Monsegur (AKA Sabu )… Hammond told Sabu a few detailed things about his life, and that was used to pin-point who he was. Hammond had been arrested before, and had told Sabu about it, which led police to put two and two together.

Link: The Down fall of LulzSec
In the case of Higinio Ochoa (my best friend), he uploaded pictures with the GPS location of his Girlfriend to his operations Twitter account. After the police identified her, they identified him through her social media accounts. In short, you need to keep your online identify completely separate from your personal life. Higz failed to follow this rule by using his girlfriend in his pictures. Yes, it was funny to see his taunting on Twitter, but they were able to use that to connect him to his crimes. Most people think that he was caught due to not understanding Exif metadata, but that is an untrue statement. One of the best ways to screw up OpSec is to rush. Deadlines are deadlines, and if you rush to meet them, you make mistakes, such as publishing the picture with metadata instead of the one you just cleaned as Higz did.
With so many possibilities and so many flaws, I think we can assume that you can never have 100% solid OpSec. If you work with anyone else, publish your victories, or communicate to others about what you’re doing, you’re at risk of fucking it up, or you’ve fucked it up already. If you look at today’s news about hackers who have gotten arrested, you will see the sentences are rising. People from other countries are being extradited to face charges in others. Groups form and break apart faster and faster, as they are infiltrated and members are turned on one another.
So in closing… listen my brothers and sisters… Practice good OpSec… or better yet… rethink what you are doing… It might not go well… Stay safe…





0 comments